Every year, thousands of people suffer from identity theft. Unlike other crimes where the damage is visible right away, victims of identity theft often don’t find out until it is too late and their life is already tragically altered. In 2020, 1.4 million people were victims of identity theft. These victims reported losses that totaled up to $3.3 billion, which is an increase from the year before which was $1.8 billion.
While most individuals think of identity theft as someone posing as a trusted authority figure, such as the IRS, and stealing information through a simple phone call, in reality, it is our internet-connected devices that make us the most vulnerable.
From computers and smartphones, all the way to the fridge, almost every device you can think of is now somehow connected to the internet. While this makes things like adding groceries to your shopping list more convenient, it also makes individuals and businesses more vulnerable, especially if they are neglecting their cybersecurity. To better protect our clients and spread awareness about this pressing issue, the team of IT experts at Integris has written this article on how to protect yourself from identity theft from hackers. Here is what you need to know:
What Is Hacking?
Hacking is a process that allows an individual, known as a hacker, to gain unauthorized access to sensitive data in a system or computer. This data is then used to commit crimes, such as theft.
As more and more people use the internet to shop, bank, and pay bills, it is opening doors for hackers to have easy access to sensitive information. This includes credit card numbers, addresses, social security numbers, etc. One hacker can cause a lot of damage by accessing just one account, as they can use that information to break into other accounts that the user may have. To make matters worse, most hackers that target users are not located within the United States and use cloaking technology to evade law enforcement, making them incredibly difficult to stop.
How Does a Hacker Get Access to My Sensitive Data?
While there are many strategies a hacker can use to get information from a user, there are two that come up most often: asking for information directly through spyware or through hacking individual websites.
The Use of Spyware
Spyware is a common tool that hackers use to get information directly from your device without you even knowing it is there. Spyware can be installed on a device through simple tricks, such as getting a user to open a spam email that has the spyware attached.
The spyware then reports back information such as keystrokes or takes pictures of the device’s screen. This allows hackers to get an inside look at your activity and potentially allows them to steal account numbers, passwords, and other sensitive information.
Hacking Individual Websites
Another common strategy that hackers use is breaking into individual websites. This can include email providers such as Google, social media, or financial institutions. Once they can hack their way in, they can then steal the information stored there.
Why Does This Information Matter For Businesses?
While hackers can target individuals and steal their identities, it is also possible for them to steal sensitive information concerning your business. If a hacker manages to get onto a device that an individual uses for both work and personal use, then not only is their identity at risk but so is your business’s sensitive data. It is extremely important to teach all employees how to protect themselves while on the web.
How to Defend Against Hackers
Performing the following can ensure that both your employees and your business’s sensitive information is secure:
Step 1: Protect Your Computers and Laptops
- Make Sure Your Devices Are Up-to-Date: Your computer’s operating system and internet-connected software, such as web browsers, will have regular updates. These updates not only help address performance issues but also help make the device more secure from evolving hacking techniques. Make sure your software is always up to date by turning on automatic updates on all of your devices.
- Use Antivirus and Antimalware Software: All computers have some type of defense against viruses, but oftentimes, it is not enough to stand up to the advanced tactics of a hacker who is determined to get in. Antivirus software, firewalls, and anti-malware should be installed on every computer and laptop to ensure that there is constant protection against hackers and harmful viruses. These programs keep up-to-date with the latest threats, helping keep you more secure and better protected.
- Disable Connections When They Are Not In Use: If you are not using your computer’s wifi or Bluetooth connectivity, turn it off. This can prevent someone who has hacked into your network from accessing your device without your knowledge.
Step 2: Protect Your Cell Phone
- Make a Strong Pin or Passcode: Cellphones are highly personal tools that many users use for pretty much everything. All of this sensitive information needs to be protected by a strong PIN or passcode.
- Only Install Trusted Apps: Apps certainly make life a lot easier and more enjoyable, but not every app should be trusted. Criminals can make up their applications that pose as a legitimate service but install malware onto your phone. Never install an app directly from the web instead, go through trusted sources such as the App Store or Google Store.
- Keep Your Software Up-to-Date: As with computers, smartphones go through regular software updates and app updates to ensure that they have stronger performance and better security.
Step 3: Protect Other Internet-Connected Devices:
- Review Your Network and Device Names: Make sure none of your devices or networks have your name on them. This makes your device more susceptible to attacks since it connects the device or network to you.
- Create Unique Passwords For All of Your Devices: When you buy a new smart device, it often comes with a simple password. Most individuals know to change the password on their phone or computer but fail to change it on their other devices, such as a smart fridge or tablet. Hackers can use these other devices to gain access to your network through them, and then use this information to hack into your phone or computer. Always change device passwords to something strong and unique for all smart devices.
Step 4: Protect Your Online Accounts

- Never Open and Delete Suspicious Emails: If you receive an email that looks questionable but it is claiming it is from a coworker, friend, or your boss, do not open it. Instead, contact that individual first and ask them about it and verify that it is from them. If they do not claim it or have no recollection, delete the email immediately.
- Use Secure Devices: Never access websites or apps that have sensitive information stored while on an unsecured network. This includes accessing these same accounts on public computers. If you have to use a public computer, fully log out when you are done.
- Create Strong Passwords For All Websites: Using strong passwords helps reduce the chances of getting hacked. It is also important to ensure that every website or account has a different password. Strong passwords need to have the following:
- At least 12 characters
- Numbers
- A special character
- Are not too predictable (such as using a pet’s or your kids’ names.)
- Use Multi-factor Authentication On Your Accounts: Multi-factor authentication often involves putting in both the password and a code that will get texted or called to your phone. This helps ensure that if you were to get hacked, the hacker can be stopped before they get into your account.
- Don’t Always Use the “Save My Information” feature: Many websites are trying to make it more convenient for users by saving your personal information, such as usernames, to use for next time. This can also be used for online shopping where the website remembers your bank information. While it is convenient, you want to only allow websites that have a URL of “https://” to remember any of this information. These URLs are secure. Always log out of the account when you are done.
- Make Sure You Have Account Alerts Turned On: A lot of email providers and social media websites will allow the user to sign up for an alert system that will tell them when their account is accessed from a new device or location. This helps protect against hackers by notifying the user immediately of potentially suspicious usage. When you get this notification, you can quickly change your password to lock out the hacker and protect your information.
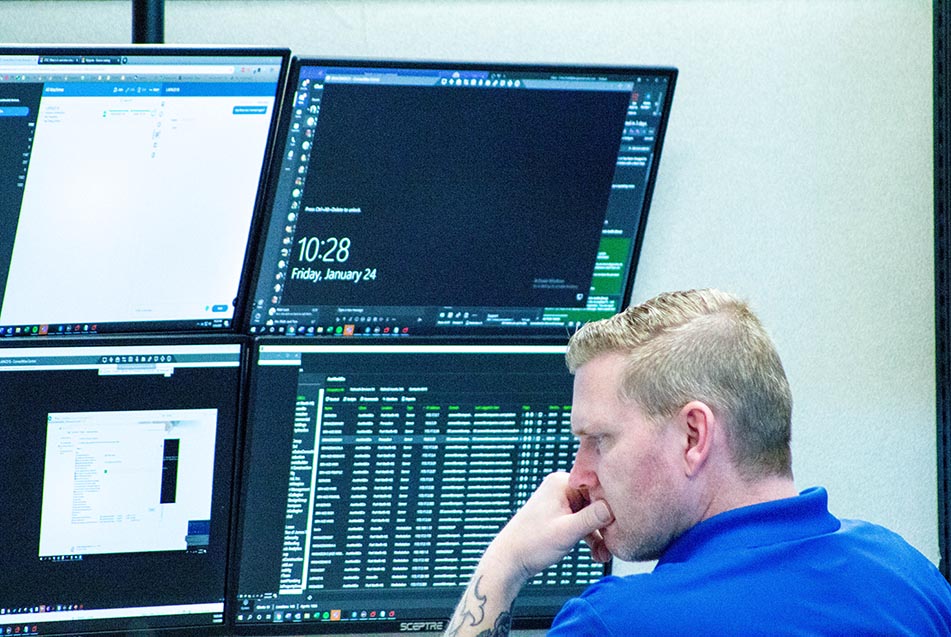
Protect Your Business and Your Employees By Partnering With Integris
Don’t risk your business or your employees’ identity and ensure that your team is properly protected against hackers by investing in cybersecurity services from Integris. Our team works hard to ensure that all of your devices and networks are secure and protected against hackers. We also offer 24/7 monitoring and proactive solutions to stop small issues before they develop into disasters. Contact our team today for more information or to schedule a consultation.



